TorZon Access Analysis
TorZon Access provides a comprehensive educational archive for researchers studying the torzon market ecosystem. This platform aggregates verified historical data, monitors uptime, and documents the cryptographic security measures used within the torzon darknet market infrastructure. We aim to provide transparency through PGP verification and architectural review.
RESEARCH NOTICE: This site is an analytical resource hub. We are not a gateway, vendor, or operator. We do not facilitate transactions.
Verified Infrastructure Mirrors
Primary Access Node
Core infrastructure endpoint. High availability verified via automated monitor.
Failover Mirrors
x33htky474572abnqhelse3ycveejfesh25symgm6oznfq35thtfukid.onion
wtcbykkm5fvvpbyr6aw4w4yyyaq2maj5zouxkt27pbufzx6lyeome4ad.onion
sgcrttmxxveqloqy2wyc62i5k755zct6d64dmvb52x5vxe46ar72zgyd.onion
Interface Architecture Analysis
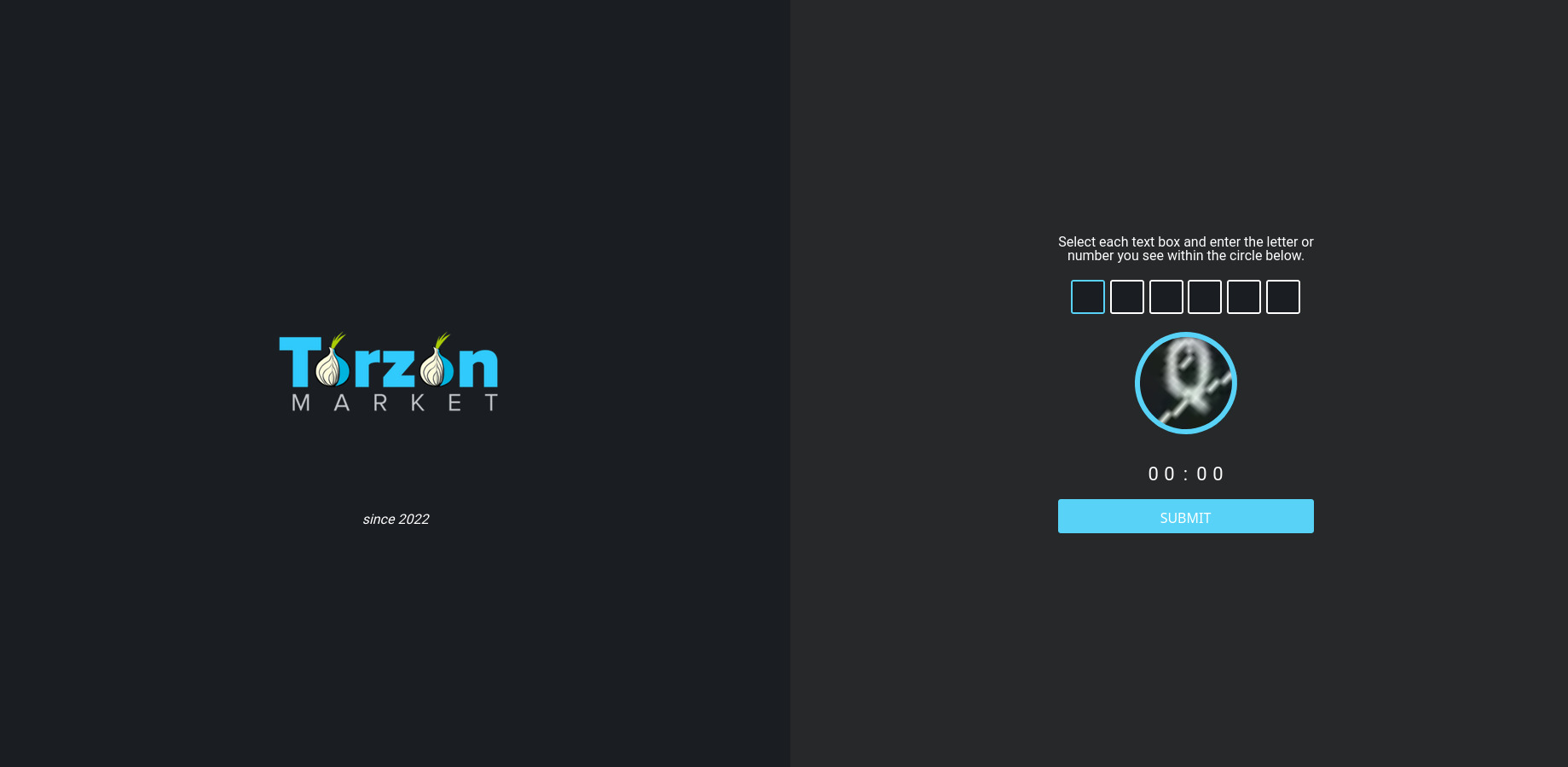
Figure 1. Automated DDoS Mitigation Layer
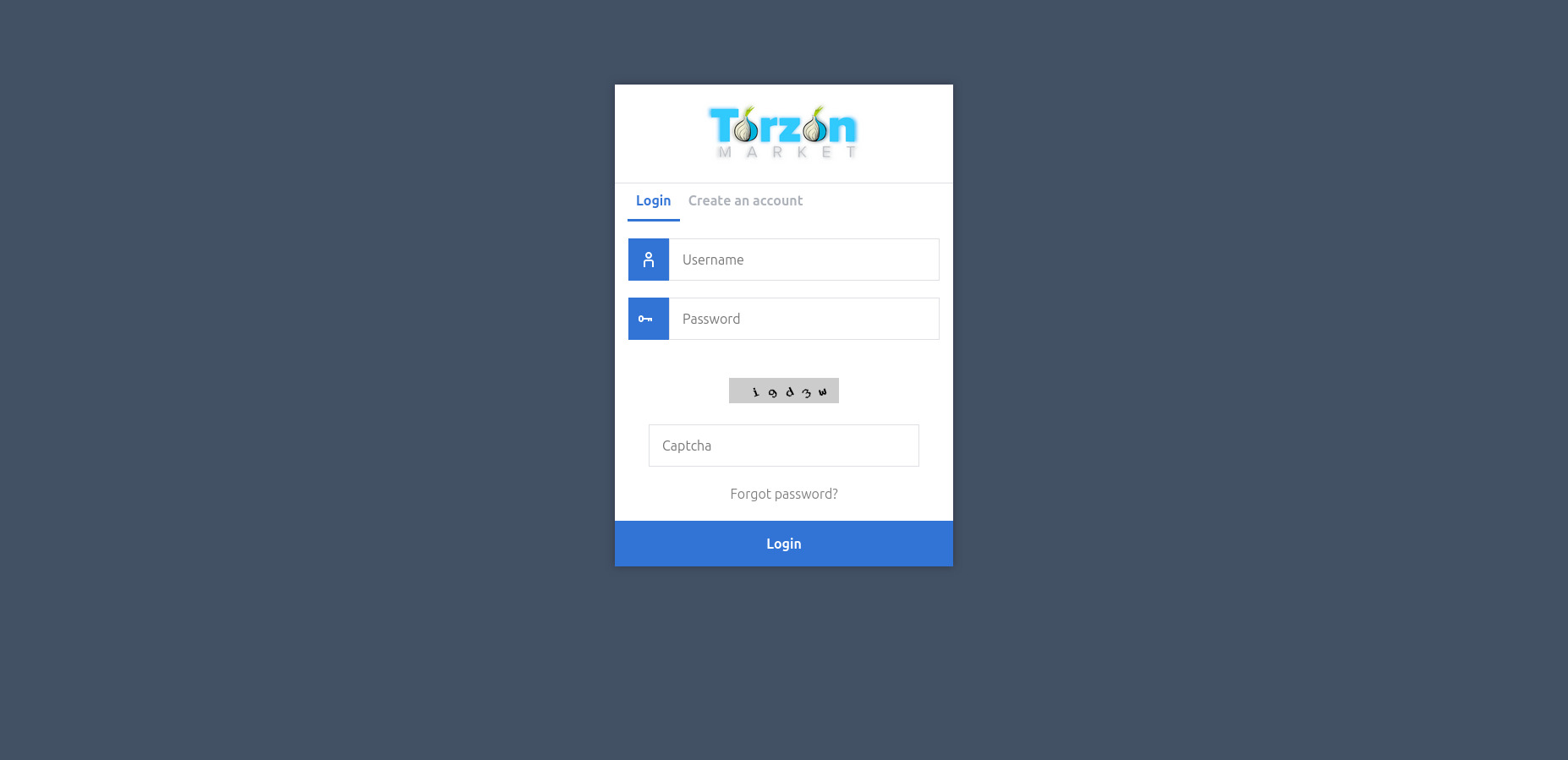
Figure 2. 2FA/PGP Login Interface
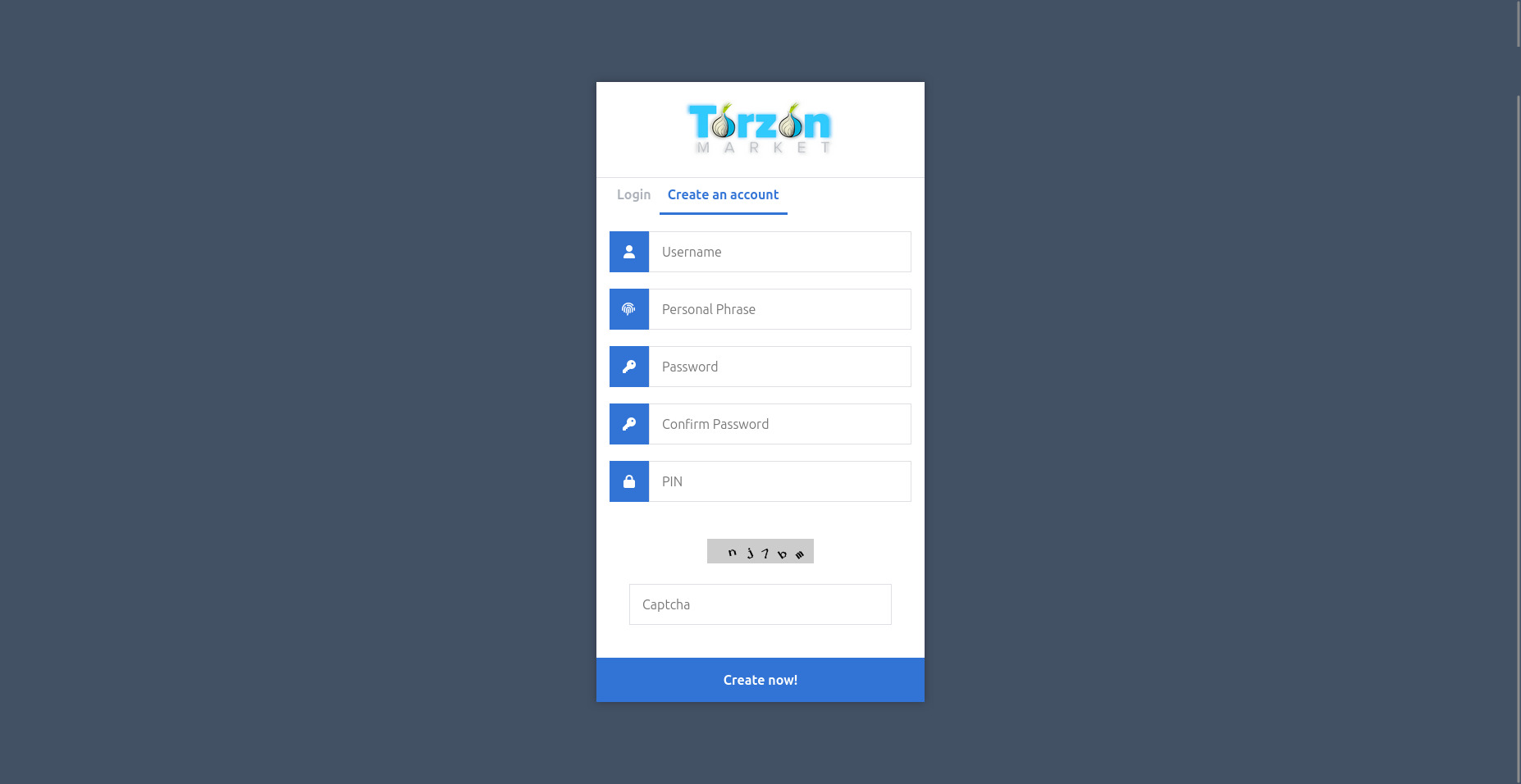
Figure 3. Anonymous Registration Protocol
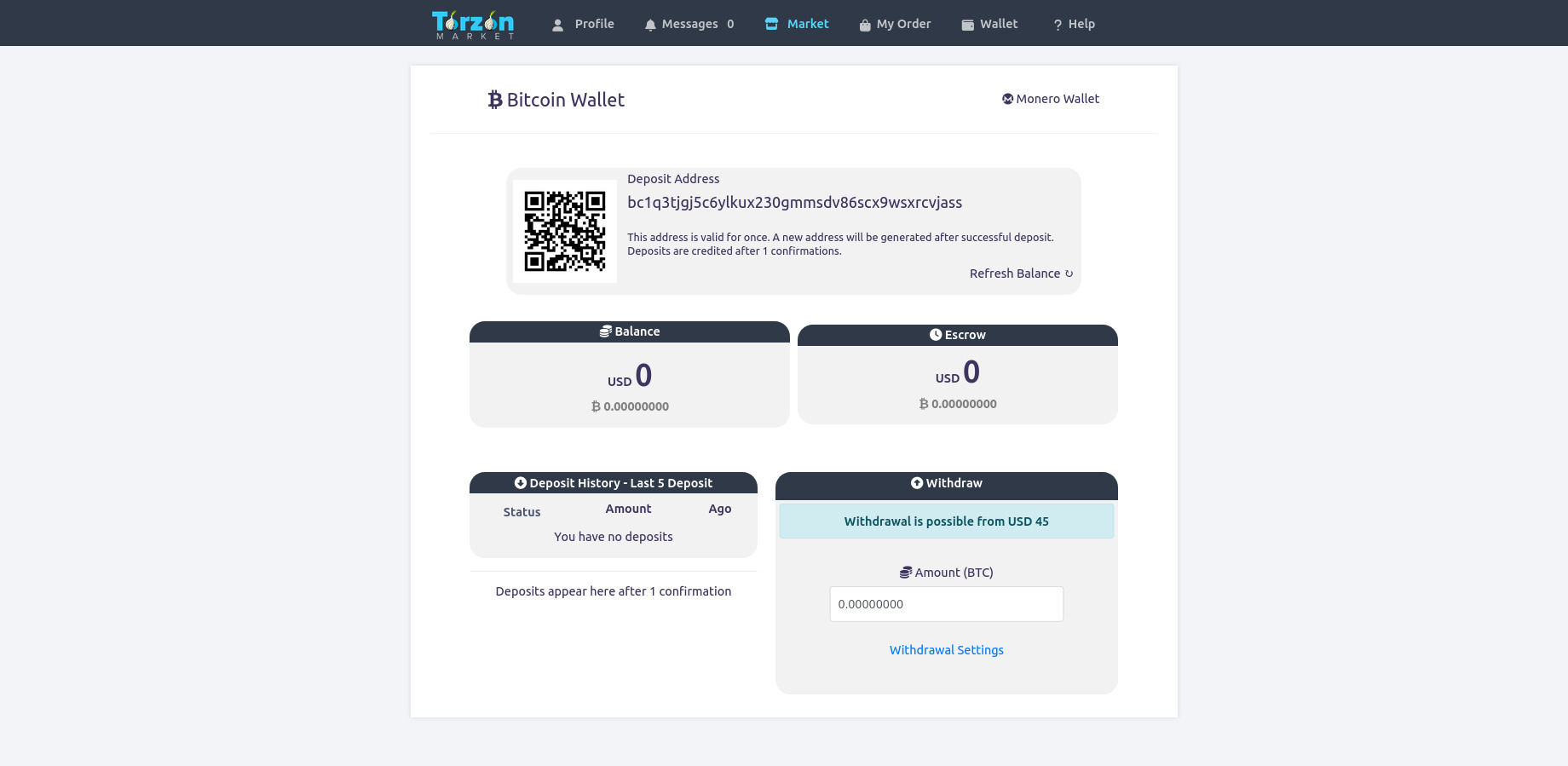
Figure 4. Central User Dashboard Overview
Research & Security Modules
Security Protocols
Detailed analysis of PGP encryption implementation and phishing defense mechanisms utilized by TorZon.
Ecosystem Guide
Educational walkthrough of the user interface, wallet systems, and operational security best practices.
Network Statistics
Historical uptime data, mirror latency reports, and cryptographic verification logs.